IEEE Std 7002 pdf download
IEEE Std 7002 pdf download IEEE Standard for Data Privacy Process
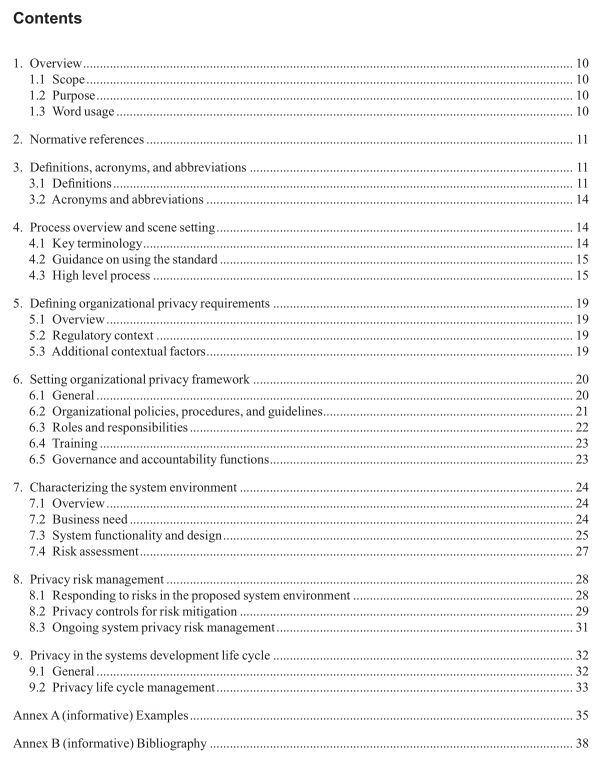
4. Process overview and scene setting
4.1 Key terminology There is often uncertainty as to the distinction between certain key, and sometimes overlapping, terms that are often used when discussing privacy, including the following:
— Data privacy and privacy. Privacy is personal and contextual, experienced by each person in a variety of different ways. Data privacy is a subset of privacy, which relates to privacy considerations that arise from the processing of data that relates to individuals.
— Data privacy and information security. The goals of data privacy and information security are overlapping in some instances and distinct in others. The goals of information security are typically characterized by preventing the loss of confdentiality, integrity, and availability. In contrast, data privacy does not have equivalent, widely agreed upon goals, although it is often related to the fair and legitimate processing of personal data. As data privacy is just a part of the wider set of privacy issues, information security is just a part of the wider feld of security. For more information about data privacy objectives, see 7.3.2.
— Data privacy and data protection. Some jurisdictions avoid the use of the term “privacy” (for instance it does not appear in the General Data Protection Regulation [GDPR]), but rather focus on the protection of data that relates to individuals, and the principles, rights, responsibilities, and obligations involved when processing personal data. While data protection laws and regulations often overlap with privacy and security issues, they are distinct. For example, group privacy, the privacy of groups as opposed to specifc individuals, might be considered an issue in data privacy, but is generally not covered in data protection law. This standard recognizes but does not intend to restate or replace applicable laws and regulations regarding personal data, data privacy, and data security. Users of this standard are responsible for referring to and observing all such laws and regulations. Conformance with the provisions of this standard does not imply compliance with any applicable legal or regulatory requirements.
— Personal data/personal information, and personally identifable information (PII). This standard uses the term “personal data,” although the standard can also apply in jurisdictions that use the term “personal information” (PII). These three terms are all used to describe information that relates to individuals. Depending on jurisdiction, different terms are used, with slightly different scopes regarding what is relatable to an individual. In applying this standard an organization should use the term or terms most appropriate for their jurisdiction(s).
— Data privacy and confdential data. Data privacy is, as previously described, related to privacy considerations that arise from the processing of data that relates to individuals. Confdential data refers to agreed upon access restrictions to data that may or may not relate to individuals. This standard looks at the process for protecting data privacy, which might incorporate the protection of confdential data as it relates to individuals but extends beyond simply protecting such confdential data. In addition to the terms covered in this subclause, 3.1 provides defnitions and further context to other key terms used in this standard.
4.2 Guidance on using the standard This standard recognizes but does not intend to restate or replace applicable laws and regulations regarding personal data, data privacy, and data security. Users of this standard are responsible for referring to and observing all such laws and regulations. Conformance with the provisions of this standard does not imply compliance with any applicable legal or regulatory requirements.
This standard addresses requirements, processes, and practices at multiple levels of the organization, from high-level policy to detailed operational procedures. This standard is designed to be applicable to a diverse set of use cases, it is iterative and modular in nature, and it will necessitate engagement (sometimes recurring engagement) from a variety of stakeholders involved in the system throughout its life cycles and user or implementer from different disciplines, at different levels, and across business lines.
Some entities may already have an organizational privacy framework in place while others may not. Those with existing frameworks in place may beneft from a gap assessment to identify what they already have in place, and what is needed to bring their frameworks into conformance with the standard. Some organizations may be developing systems for internal use, while others may be developing systems that will be used by others, possibly in other jurisdictions or industries. Those developing systems for use by others should consider not just the contextual factors that affect them, but those that may affect the users of their system. The standard is designed for iterative, recurring, and modular application, meaning that many of the actions may not happen in the order laid out or may need to be done more than once.
The choice and order of actions to be applied to a system is contingent on the organization and design of the organization’s privacy framework. At times, the user of the standard may need to repeat a process within one of the clauses or subclauses, for example a risk assessment may need to be repeated after changes to the system design. At other times users may fnd, through monitoring the wider context, organization, or system, that a change may need a response, which in turn requires further changes that cross from one section to another. For example, a change in the regulatory context, may lead to new privacy requirements that in turn affect the organizational privacy framework and system level requirements.