IEEE Std 1619.1 pdf download
IEEE Std 1619.1 pdf download IEEE Standard for Authenticated Encryption with Length Expansion for Storage Devices
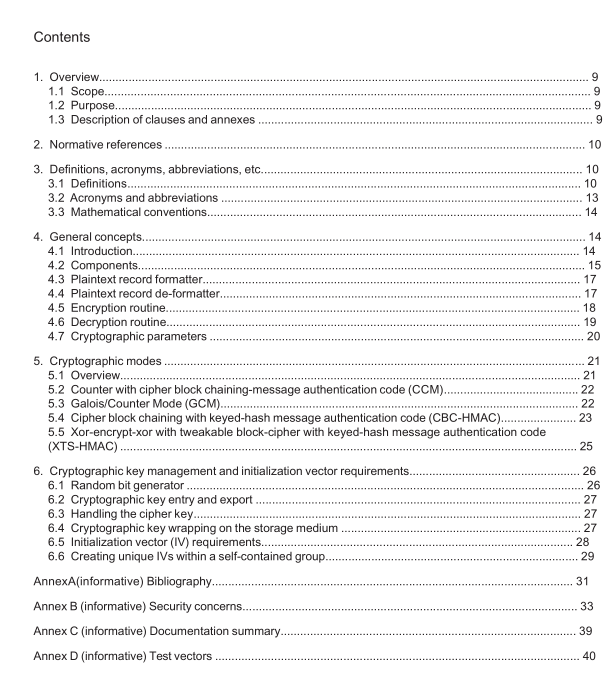
cipher block chaining with keyed-hash message authentication code (CBC-HMAC): A family of cryptographic modes that uses the cipher block chaining (CBC) mode (see NIST SP 800-38A) forconfidentiality and a key-hash message authentication code(HMAC) for integrity (see NISTFIPS 198).
cipher block chaining with keyed-hash message authentication code using secure hash algorithm(CBc-HMAC-SHA):A family of cipher blocking chaining (CBC) modes (see NIsTsP800-38A) with a keyed-hash
message authentication code (see NIST FIPs 198) from a member of the secure hash algorithm family (seeNIST FIPS 180-2).
NOTE-See 5.4.
cipher key: A bit string that controls the pseudo-random permutation of an encryption or decryption routine.See also: cryptographic key; block cipher.
ciphertext record:The result of encrypting a same-length plaintext record using a cryptographic mode ofoperation.See also: ciphertext; cryptographic mode of operation; plaintext record.
collision: An event where two independent variables have the same value in a particular context.See also:initialization vector; plaintext; ciphertext.
counter mode (CTR): A cryptographic mode of operation defined by NIST SP 800-38A inwhich the ciphertext is the bitwise exclusive-OR of the plaintext with an encrypted counter.
counter with cipher block chaining message authentication code (CCM): A cryptographic mode of operation that provides confidentiality with counter mode and integrity with a message authentication codethat uses cipher block chaining (see NIST SP 800-38C).
NOTE—See 5.2.
cryptographically-sound random-bit generator (RBG): A device or algorithm that outputs a sequence of binary bits that appears to be statistically independent and unbiased.In particular, an RBG generates numbersthat are highly unpredictable, and knowledge of any particular output from an RBG does not reveal anyinformation about other data generated by the RBG.
NOTE—See 6.1.
cryptographic hash function: A hash function that generates a hash value from an input and that has thefollowing properties: 1) it is computationally difficult to compute the inverse (i.e., compute the input from thehash value); 2) it is computationally difficult to find two different inputs that have the same hash value; 3) it iscomputationally difficult to find an input whose hash value is a particular value.
cryptographic key:Abit string used as an input into cryptographic primitives.See also: block cipher;cipher key.
cryptographic mode: See cryptographic mode of operation.
cryptographic mode of operation:An algorithm that includes a block cipher used in a particular configurationand uses a cipher key to convert plaintext into ciphertext and vice versa.See also: block cipher; cipher key,plaintext; ciphertext.
cryptographic unit: Any set of software, firmware, or hardware that can perform a cryptographic operation.decryption: The act of producing plaintext from ciphertext.Contrast: encryption.See also: plaintext;ciphertext; cryptographic key; cryptographic mode of operation.
decryption routine: An instantiation of a cryptographic mode of operation that convertsciphertext into plaintext.
encrypted record: A collection of fields that includes the output of an encryption operation or authenticationoperation (e.g, ciphertext, message authentication code), and optionally contains other information neededfor a subsequent decryption operation (e.g., additional authenticated data,initialization vector).See also:ciphertext; initialization vector; message authentication code; additional authenticated data.
encryption: The act of producing ciphertext from plaintext.Contrast: decryption. See also: plaintext;ciphertext; cryptographic key; cryptographic mode of operation.
encryption routine: An instantiation of a cryptographic mode of operation that convertsplaintext into ciphertext.
encryption session: An interval in which a cryptographic unit generates encrypted records using a set ofself-consistent variables,such as unique initialization vectors.See also: encryption; initialization vector;cryptographic unit.
NOTE—See 6.5.3.
Galois/Counter Mode (GCM): A cryptographic mode of operation that provides confidentiality throughcounter mode encryption and integrity through a message authentication code that uses Galois field arithmetic(see McGrew and Viega,The Galois/Counter Mode of Operation).
NOTE—See 5.3.
host record: A string of plaintext passed to the cryptographic unit from the host.See also: plaintext record;cryptographic unit; host.
initialization vector(IV):An input into an encryption or decryption algorithm that needs not be secret, but hasa high probability of being unique when used with a particular cipher key.See also:encryption; decryption;encryption session; cipher key.
NOTE—See 6.5.
key encrypting key (KEK): A cryptographic key used only for encrypting or decrypting other cryptographickeys.See also: cryptographic key; encryption.
keyed-hash message authentication code (HMAC): A message authentication codedefined by NIST FIPS 198 that includes a secret hash key.
key manager: Any device or person that controls the creation, archiving, and destruction of cryptographickeys.See also: cryptographic key.