ISO IEC 27555 pdf – Information security, cybersecurity and privacy protection — Guidelines on personally identifiable information deletion
ISO IEC 27555 pdf – Information security, cybersecurity and privacy protection — Guidelines on personally identifiable information deletion
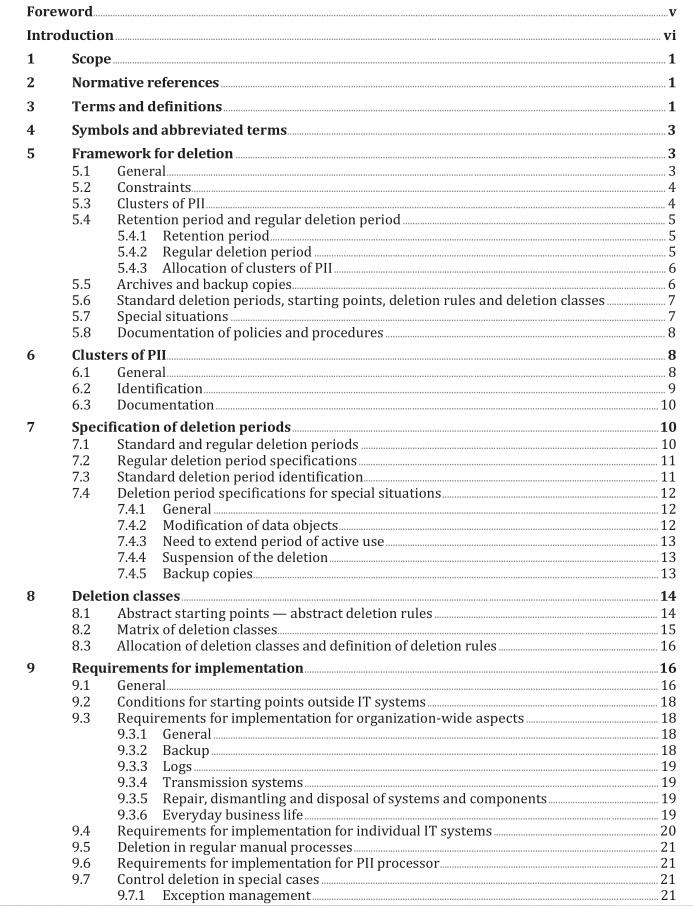
To establish deletion policies and procedures, the following steps are recommended:
— select a minimum number of standard deletion periods which form the basis of deletion classes;
— base deletion classes on the standard deletion periods identified;
— allocate each cluster of PII to a deletion class;
— identify and document the deletion procedure. The PII controller should implement deletion mechanisms for each cluster of PII based on the established policies and procedures (see 10.3).
5.2 Constraints The PII controller should establish policies and procedures for deletion of PII which enable the organization to demonstrate compliance with relevant legal, regulatory and other requirements. Where the organization is performing the role of a PII processor, they should ensure deletion rules are implemented in accordance with the relevant PII controller instructions. Where compliance and/or contractual requirements state that PII should be deleted when it is no longer required for the defined purpose, the principles contained in ISO/IEC 29100 should be considered when designing the deletion processes:
a) use, retention and disclosure limitation;
b) data minimization. EXAMPLE The deletion rule for the cluster of PII named “Accounting data” can be 10 years after the end of the financial year in which the accounting entry was made in the balance sheet. Compliance and/or contractual requirements can require special measures, particularly where clusters of PII are retained only to fulfil retention obligations. In such cases, restricting the processing of the clusters of PII concerned can be required.
5.3 Clusters of PII Clusters of PII should be named individually and unambiguously and according to their functional purposes. Each cluster of PII should be allocated one deletion rule (see 6.2). EXAMPLE For a telecommunications provider, customer data, location data, traffic data, billing data and itemized bill data are possible names of clusters of PII. The same PII can be part of more than one cluster of PII because of two cases:
— clusters of PII contain one or more data objects; NOTE Some attributes, such as name or address, can occur in several data objects in the same or different clusters of PII, e.g. in the customer master data, an invoice and a letter to the customer. Deletion is usually applied on the data object as a whole (and not on single attributes within the data object).
— copies of a data object can be part of different clusters of PII. EXAMPLE Assume an invoice documents materials and actions performed to repair an engine. Functional processes can require that three copies of the document are stored in different clusters of PII: “bookkeeping data” (deleted 11 years after payment), “engine documentation file ” to document the history and parts of the engine (deleted 5 years after destruction of the engine) and “supplier file ” to document the history of the relationship and operations with the supplier (deleted 15 years after receiving the data object). PII should not be deleted upon individual case decisions only, but in accordance with appropriate deletion rules wherever possible. Therefore, the PII controller should develop deletion rules in accordance with their deletion policy. Every deletion rule should include a definition of the deletion period and when the deletion period begins (starting point).
5.4 Retention period and regular deletion period
5.4.1 Retention period The period of time for which a cluster of PII is retained, based on its functional purposes (which can include retention period complying with business requirements as well as legal and statutory obligations), is its retention period. This time period includes the time period in which a cluster of PII is actively used in functional processes, in accordance with compliance and/or contractual purposes and in accordance with the organization’s long-term storage requirements. EXAMPLE The legal retention obligations for clusters of PII include, for example, the provisions of tax laws for trade letters and accounting documents. Functional purposes include, for example, guarantee commitments and potential equipment recall actions.
5.4.2 Regular deletion period Clusters of PII should not be deleted until the end of their defined retention period, unless specific approvals have been obtained. Legal obligations can allow for time flexibility to perform deletion after the retention period has been reached. This flexibility can be used to apply a process and mechanisms for deletion which may take into account the availability of technical solutions as well as the general organizational requirements. The combination of the retention period and the maximum time period for the deletion process is defined as the regular deletion period. The PII controller should estimate the maximum time period that is acceptable for the deletion process.